Hi, if my Neon Postgres connection string somehow leaks, are there any additional protections provided by the platform to help limit the damage? I’ve seen “restrict by IP address” (e.g. Render.com Postgres) and "add to Tailscale tailnet (e.g. Crunchy Bridge) on other platforms. Thanks!
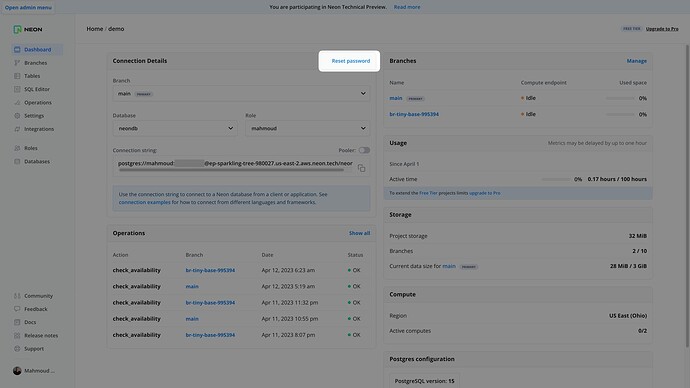
If a connection somehow leaks, you can reset the password for the connection string.
We currently don’t support restricting access to specific IP addresses. It’s on our roadmap, but not for the immediate future in Q2. Is this a blocker for you?
Okay, thanks. Yes, it’s a blocker for my use case. I’m looking to move a Heroku (Common Runtime) Postgres somewhere else for increased security.
I’ll share your feedback with our Product team. Thank you for reaching out ![]()
I agree that this is a basic security feature that should be implemented as soon as possible. Please prioritize the implementation of this feature to ensure the security of your customers’ data.
Also makes it hard for me to justify using Neon for production on my B2B SaaS, along with the general lack of information on GDPR compliance etc. Pretty much limits us to convenience for dev environments.
I would also like support for Tailscale, and the ability to restrict specific IP access per role.
Also a requirement for our use case, unfortunately. I’m glad to hear that Neon is planning on implementing this feature at least. Is there an ETA for this?
+1 for Tailscale, you guys are great!
This is a blocker for us as well, it’s a shame that this feature isn’t ready yet.
any ETA on this? would be great to have!
Hey @chachra @ogmusn @johnbeasley123 @Nick_E @net @Sukhchain_Singh @croaky
Restricting access to databases via IP address will be available by the end of the year ![]()
Btw, we also just launched the Neon Discord server. We’d love for you to join and share feedback about this feature when it lands
Thats awesome! Joined discord, thanks!
This is very great news. We are in the process of migrating our DB from render.com to NEON after learning about this.
We have also joined Discoard. I am very much looking forward to hearing the following release news before the end of the year.
Restricting access to databases via IP address will be available by the end of the year:smile:
![]() We’ve just shipped the IP Allow feature, available on Pro-tier accounts, to give you the ability to restrict access to your databases by IP and IP range.
We’ve just shipped the IP Allow feature, available on Pro-tier accounts, to give you the ability to restrict access to your databases by IP and IP range.
See Restrict Access to Your Neon Database with IP Allow - Neon for more info!